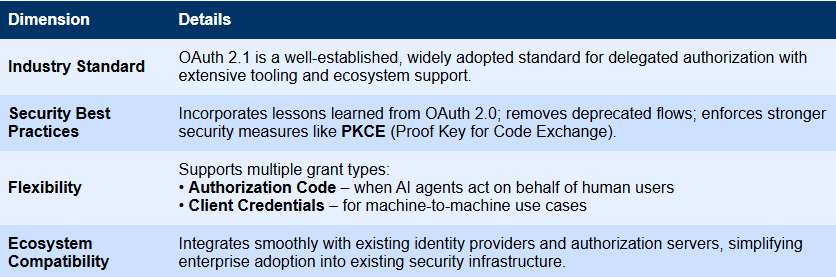
OAuth 2.1 has been established as the definitive authorization protocol within the Model Context Protocol (MCP) framework. The MCP specifications mandate that authorization servers must adopt OAuth 2.1, incorporating robust security practices tailored for both confidential and public client types.
Operating at the transport layer, MCP facilitates secure authorization, enabling clients to access protected servers on behalf of resource owners. OAuth 2.1 was selected as the foundation for MCP due to its contemporary, secure, and standardized approach to authorization management.
Understanding the MCP Authorization Process
The authorization mechanism in MCP is structured to guarantee secure and regulated access to protected resources. This process unfolds through three distinct stages:
1. Discovery Stage
When an MCP client attempts to access a secured server, the server responds with a 401 Unauthorized status code, accompanied by a WWW-Authenticate header that directs the client to the authorization server. The client then retrieves metadata from the authorization server, which outlines its capabilities and guides the client on how to proceed with authentication.
2. Authorization Stage
After acquiring the necessary information about the authorization server, the client initiates the registration and authorization sequence.
If the authorization server supports Dynamic Client Registration, the client can self-register automatically without manual intervention. During this registration, the client submits essential information such as its name, type, redirect URIs, and requested scopes. In return, the authorization server issues credentials-commonly a client_id and client_secret-which the client will use in future interactions. This automation streamlines onboarding, especially beneficial in environments with numerous or automated clients.
Following registration, the client proceeds with the appropriate OAuth flow based on its use case:
- Authorization Code Flow: Employed when acting on behalf of an end-user, requiring user consent.
- Client Credentials Flow: Utilized for secure server-to-server communication without user involvement.
In the Authorization Code Flow, the user grants permission, after which the authorization server issues an access token scoped to the client’s permissions.
3. Access Stage
Armed with the access token, the client includes it in requests to the MCP server. The server validates the token’s authenticity and scope before processing the request and returning the response. Each transaction is meticulously logged to ensure auditability and compliance, reinforcing security and traceability.
Enhanced Security Features in MCP’s OAuth 2.1 Implementation
The MCP OAuth 2.1 specification integrates several critical security improvements designed to fortify the authorization process:
Enforced Use of PKCE
All MCP clients are required to implement Proof Key for Code Exchange (PKCE), a security extension that generates a unique “verifier-challenge” pair. This mechanism ensures that only the client initiating the authorization request can exchange the authorization code for tokens, effectively mitigating risks such as code interception or injection attacks.
Strict Redirect URI Enforcement
Clients must pre-register their exact redirect URIs with the authorization server. During authorization, the server verifies that the redirect URI in the request matches the registered URI precisely, preventing attackers from redirecting tokens to malicious endpoints.
Short-Lived Access Tokens
Authorization servers are encouraged to issue access tokens with limited lifespans. This approach minimizes the window of opportunity for misuse if tokens are compromised, enhancing overall security.
Fine-Grained Scope Control
MCP OAuth 2.1 supports detailed permission scopes, allowing clients to request only the access they require. Examples of such scopes include:
mcp:tools:climate– Grants access exclusively to climate-related tools.mcp:data:client-info:read– Provides read-only access to client information.mcp:operations:automation:*– Authorizes execution of any automation workflow.
Automated Client Registration
Dynamic Client Registration enables MCP clients and servers to automate the issuance of client credentials, eliminating manual setup. This capability accelerates the secure onboarding of new AI agents and other clients.
Implementing OAuth 2.1 in MCP Servers: A Practical Guide
In the upcoming section, we will explore a hands-on implementation of OAuth 2.1 within MCP servers. Using a sample financial sentiment analysis server, we will demonstrate how to integrate authorization seamlessly with Scalekit, a tool designed to simplify OAuth workflows and enhance security.