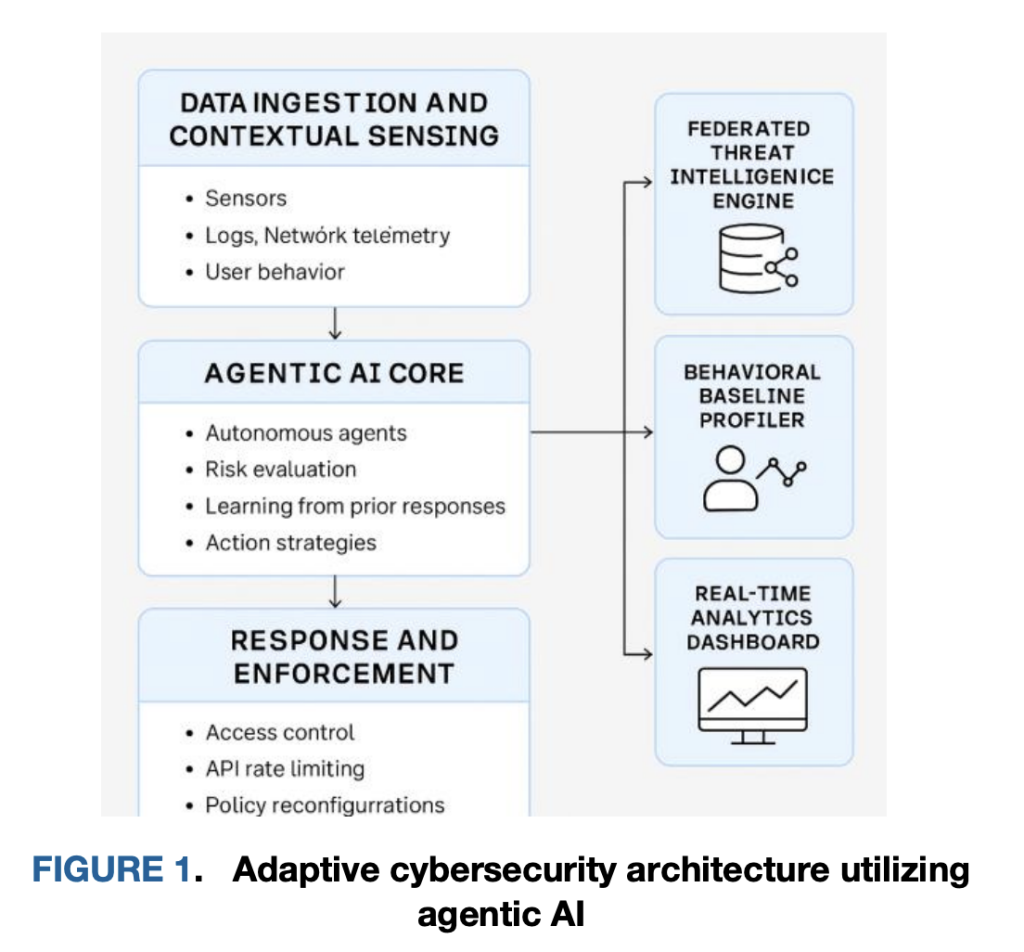
Is it possible for your AI-driven security framework to detect, analyze, and mitigate an active cyber threat in approximately 220 milliseconds-without relying on a centralized feedback loop? Researchers from Google and the University of Arkansas at Little Rock have introduced an innovative agent-based cybersecurity “immune system” composed of lightweight, autonomous AI sidecar agents deployed alongside workloads such as Kubernetes pods, API gateways, and edge services. Rather than funneling raw telemetry data to a centralized SIEM for batch processing, each agent independently establishes behavioral baselines, identifies anomalies through federated intelligence sharing, and enforces least-privilege mitigations directly at the execution point. In a controlled cloud-native environment, this edge-centric approach reduced the time from detection to mitigation to roughly 220 ms-about 3.4 times faster than traditional centralized systems-while achieving an F1 score near 0.89 and maintaining host resource consumption below 10% CPU and RAM. These findings demonstrate that integrating detection and enforcement within the workload plane can significantly enhance responsiveness and accuracy without imposing substantial resource costs.
Decoding the “Profile → Reason → Neutralize” Cycle in AI-Driven Security
Behavioral Profiling at the Edge
These AI agents operate as sidecars or daemonsets adjacent to microservices and API gateways, continuously constructing detailed behavioral profiles based on execution traces, system call sequences, API interactions, and inter-service communication patterns. Unlike static allowlists or threshold-based monitoring, this profiling adapts dynamically to ephemeral workloads, rolling updates, and autoscaling events-scenarios that often undermine traditional perimeter defenses. The profiling process captures not only quantitative metrics but also structural characteristics such as event order, timing, and peer relationships, enabling the detection of novel, zero-day-like anomalies. This continuous, context-sensitive baseline is tailored per workload and identity boundary, ensuring that “normal” behavior is learned in situ.
Intelligent Reasoning with Federated Insights
Upon detecting suspicious activity-such as an unexpected surge of encrypted data uploads from a low-trust entity or an unfamiliar API call graph-the local agent synthesizes anomaly scores with federated intelligence. This federated intelligence comprises shared indicators and incremental model updates exchanged among peer agents, enhancing detection accuracy without centralized bottlenecks. The reasoning process is designed to be edge-first, enabling autonomous risk assessments without round-trips to a central authority. This continuous, request-level evaluation aligns with zero-trust principles by assessing identity and context dynamically, rather than relying on static session-based permissions, thereby reducing latency and minimizing attack surface exposure.
Swift and Precise Threat Neutralization
When the calculated risk surpasses a context-aware threshold, the agent promptly enacts local mitigations aligned with least-privilege principles. These actions include quarantining containers (pausing or isolating), rotating credentials, enforcing rate limits, revoking tokens, or tightening route-specific policies. All enforcement actions are logged with clear, human-readable explanations and synchronized back to policy repositories for audit and compliance. The rapid response capability-triggering mitigations in approximately 220 ms compared to 540-750 ms in centralized or firewall-based systems-translates to a 70% reduction in latency, significantly limiting the window for lateral movement within the network.
Empirical Validation: Performance Benchmarks and Baselines
The proposed architecture was rigorously tested in a Kubernetes-native simulation environment that emulated API abuse and lateral movement attack scenarios. Compared to two standard baselines-(i) static rule-based pipelines and (ii) batch-trained machine learning classifiers-the agentic framework demonstrated superior performance with a Precision of 0.91, Recall of 0.87, and an F1 score of 0.89. In contrast, static rules and baseline ML models achieved F1 scores of approximately 0.64 and 0.79, respectively. Decision-to-mitigation latency was reduced to around 220 ms for local enforcement, whereas centralized approaches required between 540 and 750 ms due to coordination overhead. Importantly, the system maintained host resource utilization below 10% for CPU and RAM, underscoring its operational efficiency.
Implications for Zero-Trust Architecture and Real-World Deployment
Advancing Zero-Trust with Autonomous Edge Enforcement
Zero-trust security mandates continuous, request-level verification based on identity, device posture, and contextual factors. However, many existing zero-trust implementations still rely on centralized policy engines, which introduce latency and potential bottlenecks under heavy load. By relocating risk assessment and enforcement to autonomous edge agents, this architecture transforms zero-trust from periodic policy pulls into a network of self-sufficient, continuously learning controllers. These controllers apply least-privilege mitigations locally and synchronize state asynchronously, reducing mean time to contain (MTTC) threats and confining decisions within the immediate threat radius-critical when inter-pod communication occurs within milliseconds. Additionally, the federated sharing mechanism enables privacy-conscious distribution of threat indicators and model updates, which is particularly beneficial for multi-tenant SaaS environments and compliance with data protection regulations.
Seamless Integration with Kubernetes, API Gateways, and Identity Providers
Operationally, the AI agents are deployed alongside workloads as sidecars or node-level daemons. Within Kubernetes clusters, they tap into CNI telemetry for network flow data, container runtime events for process-level insights, and API gateway traces (e.g., Envoy or NGINX) for request graph analysis. Identity information is ingested from identity providers (IdPs), enabling the computation of continuous trust scores that incorporate recent behavioral patterns and environmental context such as geographic risk and device health. Mitigation actions are implemented as idempotent primitives-network micro-policy adjustments, token revocations, per-route quotas-allowing for incremental tightening or rollback. The control loop-sense, reason, act, learn-is fully feedback-driven and supports both autonomous operation for low-risk interventions and human-in-the-loop workflows for high-impact changes, including policy windows and approval gates.
Governance, Transparency, and Safety Mechanisms
Rapid response capabilities must be balanced with auditability, especially in regulated industries. The system emphasizes explainable decision logs that document the signals and thresholds triggering each action, alongside signed and versioned policy and model artifacts to ensure traceability. Privacy-preserving modes are supported, enabling sensitive data to remain local while sharing only model updates; differential privacy techniques are proposed for environments with stringent data protection requirements. Safety features include override and rollback capabilities, as well as staged rollouts such as canary deployments of new mitigation templates in non-critical namespaces. These safeguards align with emerging best practices for agentic security systems, underscoring the importance of threat modeling and operational guardrails when deploying autonomous multi-agent pipelines.
From Simulation to Production: Practical Considerations
The evaluation was conducted over a 72-hour cloud-native simulation incorporating injected attack behaviors like API misuse, lateral movement, and zero-day-like anomalies. Real-world deployments will encounter additional complexities such as noisy telemetry, multi-cluster networking, and heterogeneous CNI plugins, which may impact detection accuracy and enforcement latency. Nevertheless, the core architecture-local decision-making coupled with immediate local action-is topology-agnostic and expected to maintain order-of-magnitude improvements in latency, provided that mitigations are mapped to primitives supported by the runtime environment. For production rollout, a phased approach is recommended: start with observe-only agents to establish behavioral baselines, enable mitigations for low-risk actions (e.g., quota enforcement, token revocation), and progressively gate high-impact controls (e.g., network segmentation, container quarantine) behind policy windows until confidence metrics stabilize.
Positioning Within the Evolving Agentic Security Ecosystem
Research into securing autonomous agent systems and leveraging agent workflows for cybersecurity is rapidly expanding. The presented work focuses on defense through agent autonomy situated close to workloads. Complementary efforts address threat modeling for agentic AI, secure inter-agent communication protocols, and vulnerability testing of autonomous agents. Organizations adopting this architecture should integrate it with contemporary agent-security threat models and employ rigorous test harnesses to evaluate agent tool-use boundaries and memory safety, ensuring robust and secure deployments.
Performance Comparison: Kubernetes Simulation Results
| Metric | Static Rules Pipeline | Baseline ML (Batch Classifier) | Agentic Framework (Edge Autonomy) |
|---|---|---|---|
| Precision | 0.71 | 0.83 | 0.91 |
| Recall | 0.58 | 0.76 | 0.87 |
| F1 Score | 0.64 | 0.79 | 0.89 |
| Decision-to-Mitigation Latency | ~750 ms | ~540 ms | ~220 ms |
| Host Overhead (CPU/RAM) | Moderate | Moderate | <10% |
Essential Insights
- Edge-First Cybersecurity Immune System: Deploying lightweight AI agents as sidecars or daemons alongside workloads enables local behavioral learning, autonomous decision-making, and enforcement of least-privilege mitigations without dependence on centralized SIEM systems.
- Superior Performance Metrics: Achieves decision-to-mitigation times around 220 ms-approximately 3.4 times faster than centralized pipelines-with an F1 score near 0.89 in Kubernetes-based simulations.
- Minimal Resource Impact: Maintains host CPU and RAM usage below 10%, ensuring suitability for microservices and edge computing environments.
- Continuous Profile → Reason → Neutralize Loop: Agents perpetually baseline normal activity, integrate local and federated signals for risk assessment, and apply immediate, reversible controls such as container quarantine, token rotation, and rate limiting.
- Alignment with Zero-Trust Principles: Implements continuous, context-aware decision-making based on identity, device posture, and environment, replacing static role-based access controls and reducing dwell time and lateral movement risks.
- Robust Governance and Safety: Ensures all actions are logged with transparent rationales; policies and models are cryptographically signed and versioned; high-impact mitigations are subject to human oversight and staged deployment.
Conclusion
This research advocates for a distributed defense model composed of autonomous agents that profile, reason, and neutralize threats directly where they emerge. The demonstrated metrics-~220 ms response times, a 3.4× speedup over centralized baselines, an F1 score of approximately 0.89, and under 10% resource overhead-highlight the benefits of eliminating central coordination delays and empowering local autonomy for least-privilege enforcement. This approach dovetails with zero-trust’s continuous verification ethos and offers a pragmatic pathway toward self-stabilizing security operations: continuously learn normal behavior, detect deviations enriched by federated context, and contain threats swiftly before they propagate beyond control boundaries.